Ethereum Revives TheDAO With $220 Million Security Fund
Ethereum’s infamous DAO hack from 2016 is being transformed into a long-term security asset, as $220 million worth of unclaimed ETH is repurposed into a new decentralized security fund.
Key Takeaways
- Around 75,000 ETH, linked to the 2016 DAO hack, will fund Ethereum security projects.
- 69,420 ETH will be staked, generating approximately $8 million annually for grants.
- Governance will follow DAO-style mechanisms like quadratic and retroactive funding.
- The move marks a symbolic and practical return to DAO coordination nearly 10 years later.
What Happened?
A group of early Ethereum contributors, including Vitalik Buterin and Griff Green, have launched a major security initiative repurposing 2016 DAO hack funds. The new project, dubbed The DAO Fund, will turn unclaimed assets into a renewable funding source for Ethereum security and governance.
Ethereum’s Biggest Hack Now Fuels Its Defense
In 2016, The DAO was a groundbreaking but flawed experiment in decentralized governance. Built on Ethereum, it attracted one of the largest crowdsales in crypto history, raising over $150 million. Just months later, a bug in its smart contracts allowed a hacker to drain around $60 million in ETH, shaking the network’s foundations.
The Ethereum community was divided on how to respond. A hard fork was implemented to roll back the damage, but not all users agreed, leading to the creation of Ethereum Classic. Despite the fork, tens of thousands of ETH remained unclaimed, either due to user error, lost keys, or overlooked claims.
Today, those dormant assets have grown in value and are now being reintegrated into the ecosystem as a proactive solution rather than a lingering problem.
Fund Breakdown and Structure
The $220 million security fund will be sourced from two main pools:
- ExtraBalance Pool: About 70,500 ETH remained from DAO investors who paid above the 1 ETH per 100 DAO token cap. These excess funds were unclaimed after the hard fork.
- Curator Multisig Wallet: Holds roughly 4,600 ETH, originally collected from DAO tokens stuck in faulty contracts.
Out of this, 69,420 ETH will be staked, creating a yield-based endowment expected to return $8 million per year in staking rewards. This yield will be distributed to Ethereum security initiatives on a recurring basis.
How the Grants Will Be Distributed?
Grants will be allocated through DAO-native governance tools, giving the community direct involvement. The distribution methods include:
- Quadratic funding to support broad-based community projects.
- Retroactive funding for completed and impactful security work.
- Ranked-choice RFP voting to prioritize proposals based on collective preferences.
Eligibility will be managed by the Ethereum Foundation, with operational help from public goods group Giveth, co-founded by Griff Green. Open applications will allow external operators to participate, ensuring transparency and minimizing centralization risks.
A Symbolic Revival for TheDAO
Nearly a decade after TheDAO’s collapse fractured the Ethereum community, its remaining assets are being used to strengthen the very thing it once put at risk: Ethereum’s security culture. As Griff Green noted, the DAO hack catalyzed Ethereum’s audit industry and changed how the ecosystem views smart contract safety.
Green said on the Unchained podcast:
With Ethereum now securing hundreds of billions of dollars, the timing of this initiative highlights the importance of long-term investment in protocol safety and user protection.
CoinLaw’s Takeaway
In my experience, crypto rarely gets a second chance to right a wrong. But this is one of those rare times. Taking unclaimed funds from Ethereum’s most infamous hack and turning them into a perpetual, DAO-governed security endowment is both poetic and practical. I find it inspiring that the same community that once split over a crisis is now uniting to build a safer future using the very assets that caused so much division. This is crypto maturity in action.
The post Ethereum Revives TheDAO With $220 Million Security Fund appeared first on CoinLaw.
You May Also Like

The Stunning ASEAN Winner Emerges As Manufacturing Shifts Accelerate
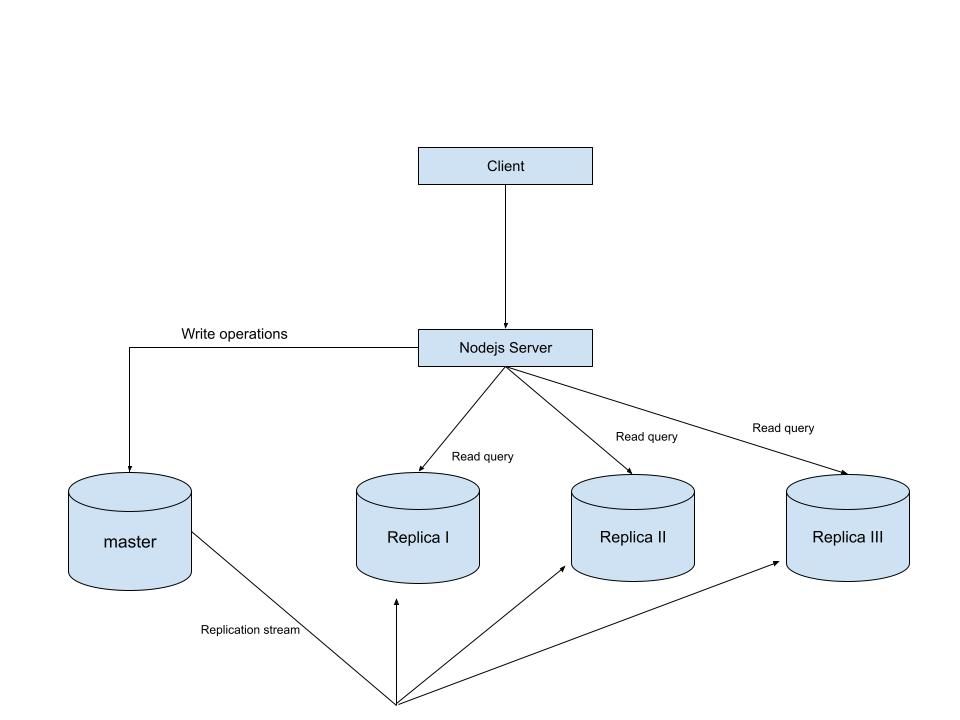
MySQL Single Leader Replication with Node.js and Docker
command: --server-id=1 --log-bin=ON The --server-id option gives each MySQL server in your replication setup its own name tag. Each one has to be unique and without it, replication won’t work at all. Another cool option not included here is binlog_format=ROW. This tells MySQL how to keep track of changes before passing them along to the replicas. By default, MySQL already uses row-based replication, but you can explicitly set it to ROW to be sure or switch it to STATEMENT if you’d rather log the actual SQL statements instead of row-by-row changes. \ Run our containers on docker Now, in the terminal, we can run the following command to spin up our database containers: docker-compose up -d \ Setting Up Our Master (Primary) Server To configure our master server, we would have to first access the running instance on docker using the following command docker exec -it mysql-master bash This command opens an interactive Bash shell inside the running Docker container named mysql-master, allowing us to run commands directly inside that container. \ Now that we’re inside the container, we can access the MySQL server and start running commands. type: mysql -uroot -p This will log you into MySQL as the root user. You’ll be prompted to enter the password you set in your docker-compose.yml file. \ Next, we need to create a special user that our replicas will use to connect to the master server and pull data. Inside the MySQL prompt, run the following commands: \ CREATE USER 'repl_user'@'%' IDENTIFIED BY 'replication_pass'; GRANT REPLICATION SLAVE ON . TO 'repl_user'@'%'; FLUSH PRIVILEGES; Here’s what’s happening: CREATE USER makes a new MySQL user called repl_user with the password replication_pass. GRANT REPLICATION SLAVE gives this user permission to act as a replication client. FLUSH PRIVILEGES tells MySQL to reload the user permissions so they take effect immediately. \ Time to Configure the Replica (Secondary) Servers a. First, let’s access the replica containers the same way we did with the master. Run this command in your terminal for each of the replica containers: \ docker exec -it <replica_container_name> bash mysql -uroot -p <replica_container_name> should be replace with the name of the replica container you are trying to setup b. Now it’s time to tell our replica where to get its data from. While inside the replica’s MySQL shell, run the following command to configure replication using the master’s details: CHANGE REPLICATION SOURCE TO SOURCE_HOST='mysql-master', SOURCE_USER='repl_user', SOURCE_PASSWORD='replication_pass', GET_SOURCE_PUBLIC_KEY=1; With the replication settings in place, let’s fire up the replica and get it syncing with the master. Still inside the MySQL shell on the replica, run: START REPLICA; This starts the replication process. To make sure everything is working, check the replica’s status with:
SHOW REPLICA STATUS\G; Look for Replica_IO_Running and Replica_SQL_Running — if both say Yes, congratulations! 🎉 Your replica is now successfully connected to the master and replicating data in real time.
Testing Our Replication Setup from the Node.js App Now that our replication is successfully set up, we can configure our Node.js server to observe the real-time effect of data being replicated from the master server to the replica server whenever we write to it. We start by installing the following dependencies:
npm i express mysql2 sequelize \ Now create a folder called src in the root directory and add the following files inside that folder connection.js, index.js and model.js. Our current directory should look like this We can now set up our connections to our master and replica server in the connection.js file as shown below
const Sequelize = require("sequelize"); const sequelize = new Sequelize({ dialect: "mysql", replication: { write: { host: "127.0.0.1", username: "root", password: "master", database: "replicaDb", }, read: [ { host: "127.0.0.1", username: "root", password: "slave", database: "replicaDb", port: 3307 }, { host: "127.0.0.1", username: "root", password: "slave", database: "replicaDb", port: 3308 }, { host: "127.0.0.1", username: "root", password: "slave", database: "replicaDb", port: 3309 }, ], }, }); async function connectdb() { try { await sequelize.authenticate(); } catch (error) { console.error("❌ unable to connect to the follower database", error); } } connectdb(); module.exports = { sequelize, }; \ We can now create a User table in the model.js file
const {DataTypes} = require("sequelize"); const { sequelize } = require("./connection"); const User = sequelize.define("User", { name: { type: DataTypes.STRING, allowNull: false, }, email: { type: DataTypes.STRING, unique: true, allowNull: false, }, }); module.exports = User \ and finally in our index.js file we can start our server and listen for connections on port 3000. from the code sample below, all inserts or updates will be routed by sequelize to the master server. while all read queries will be routed to the read replicas.
const express = require("express"); const { sequelize } = require("./connection"); const User = require("./model"); const app = express(); app.use(express.json()); async function main() { await sequelize.sync({ alter: true }); app.get("/", (req, res) => { res.status(200).json({ message: "first step to setting server up", }); }); app.post("/user", async (req, res) => { const { email, name } = req.body; let newUser = await User.build({ name, email, }); // This INSERT will go to the write (master) connection newUser = newUser.save({ returning: false }); res.status(201).json({ message: "User successfully created", }); }); app.get("/user", async (req, res) => { // This SELECT query will go to one of the read replicas const users = await User.findAll(); res.status(200).json(users); }); app.listen(3000, () => { console.log("server has connected"); }); } main(); When you make a POST request to the /users endpoint, take a moment to check both the master and replica servers to observe how data is replicated in real time. Right now, we are relying on Sequelize to automatically route requests, which works for development but isn’t robust enough for a production environment. In particular, if the master node goes down, Sequelize cannot automatically redirect requests to a newly elected leader. In the next part of this series, we’ll explore strategies to handle these challenges